Blog
Discover our latest articles and blogs

Essential proxy detection tips for stronger network security
Discover the top proxy detection techniques for 2026, compare methods side by side, and learn how to select the right strategy for your network environment.
Geo-IP intelligence: security, privacy, and risk in 2026
Learn how geo-IP intelligence works, its role in cybersecurity and fraud prevention, and the privacy risks businesses and individuals must manage in 2026.
Why IP addresses matter: privacy, security and connectivity
Discover why IP addresses matter for your privacy, security and connectivity. Learn how IPv4, IPv6, NAT and IP leaks affect you and your business online.

How to interpret IP lookup results for network security
Learn how to interpret IP lookup results accurately, using reputation scores, ASN data, and proxy flags to strengthen network security and reduce false positives.
Monitor your public IP: boost cybersecurity and network stability
Learn how to monitor your public IP address to strengthen cybersecurity, prevent breaches, and maintain network stability for your business in 2026.
Public IP checklist: secure, monitor and troubleshoot in 5 steps
A step-by-step public IP address checklist for IT teams: reduce exposure, verify security controls, check blacklists, and fix geolocation issues with confidence.

Essential IP address privacy tips to protect your data
Learn how to protect your IP address privacy with expert tips on VPNs, leak testing, and browser settings to safeguard your personal data online.
Understand ISP tracking: real-world examples and privacy tips
Discover how ISPs track your online activity via DNS, DPI, and metadata, with real-world examples and practical privacy steps to reduce your exposure.
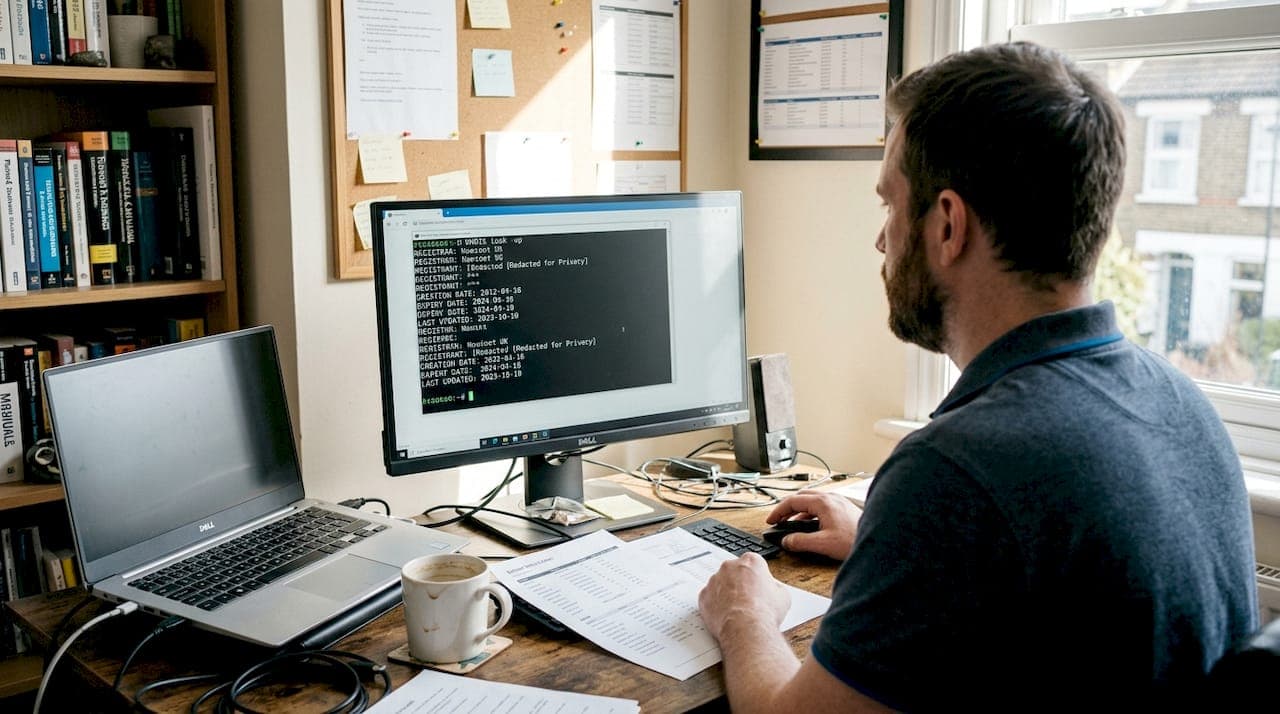
WHOIS lookup: key tool for security and privacy in 2026
Learn how WHOIS lookup works, who uses it, and why it matters for domain security, privacy, and online threat investigation in 2026.