Many people believe IP addresses are just random numbers assigned by their internet provider. In reality, they're the fundamental addressing system that makes every online interaction possible. Without them, your device couldn't send an email, load a webpage, or stream a video. Understanding IP addresses unlocks insights into how the internet functions, why your privacy matters, and how cybersecurity professionals protect networks. This guide explains what IP addresses are, their types and versions, their role in security, and the infrastructure challenges shaping internet connectivity today.
Table of Contents
- Key takeaways
- What is an IP address and how does it function?
- Different types and versions of IP addresses explained
- The role of IP addresses in cybersecurity and online privacy
- How IP address allocation and transfers impact internet infrastructure
- Explore IP lookup tools to enhance your understanding
- What is an IP address?
Key Takeaways
| Point | Details |
|---|---|
| Definition and role | An IP address uniquely identifies a device on a network and provides its location for routing traffic. |
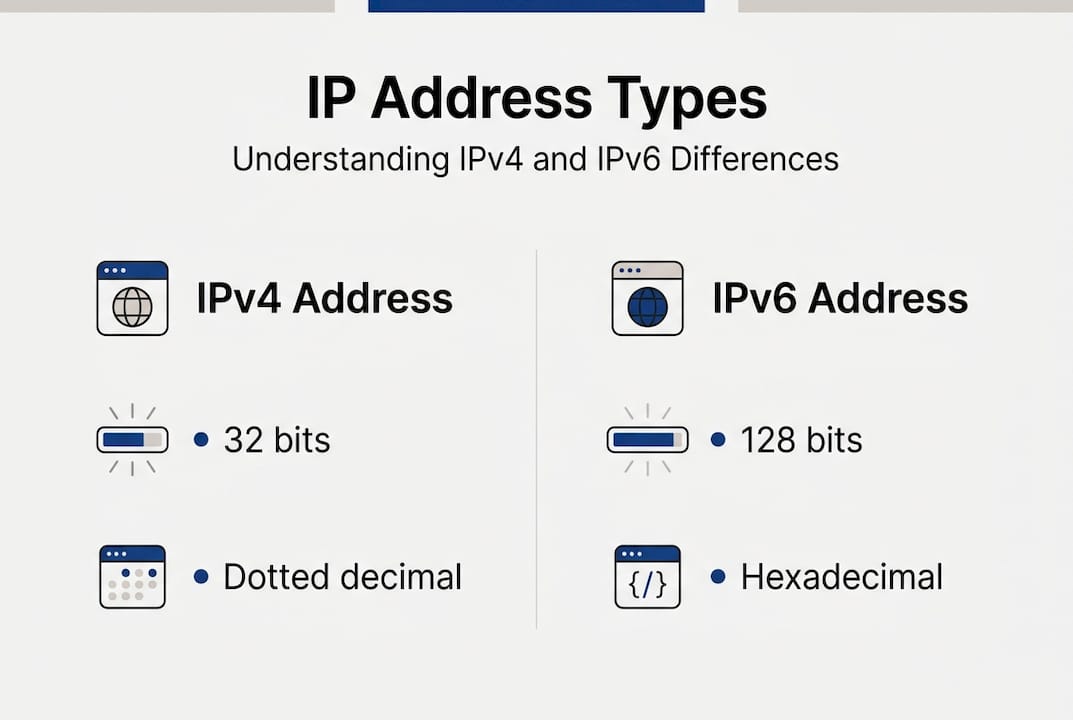
| IPv4 versus IPv6 | IPv4 uses 32 bits and dotted decimal notation, providing about 4.3 billion addresses, while IPv6 uses 128 bits and hexadecimal notation offering vastly more addresses. |
| Public versus private | Public addresses are reachable on the internet while private addresses are used inside local networks and require translation to access the internet. |
| Static versus dynamic | Dynamic addressing reuses addresses to conserve IPv4 space, while static addresses remain fixed for reliable services. |
| Security and privacy | IP addresses underpin cybersecurity and privacy by revealing who connects to whom and enabling protective measures. |
What is an IP address and how does it function?
An IP address is a unique numerical label assigned to every device connected to a network using the Internet Protocol for communication, serving to identify the host or network interface and provide its location for routing traffic. Think of it as a postal address for your computer, smartphone, or any device that connects to the internet. Just as mail needs a street address to reach your home, data packets need an IP address to find their destination across networks.
When you visit a website, your device sends a request containing your IP address as the source and the web server's IP address as the destination. Routers across the internet examine these addresses in packet headers and forward the data along the most efficient path. This process happens billions of times per second globally, enabling everything from video calls to online banking. Without IP addresses, devices would have no way to identify each other or establish connections.
Every IP address serves two critical functions. First, it identifies the specific device or network interface requesting or receiving data. Second, it provides location information that routers use to direct traffic efficiently. When you understand IP addresses, you gain insight into how networks maintain order despite handling massive data volumes simultaneously.
The technical structure varies between IP versions, but the core principle remains consistent. An IPv4 address like 192.168.1.1 uses four decimal numbers separated by periods, each representing eight bits of data. This dotted decimal notation makes addresses human readable whilst maintaining the binary format computers require. Modern networks rely on this addressing system to maintain connectivity and ensure data reaches intended recipients.
Pro Tip: Your device likely has multiple IP addresses simultaneously. Your router assigns a private IP for local network communication whilst your ISP provides a public IP for internet access.
Consider these fundamental aspects of IP addressing:
- IP addresses enable device identification across local and global networks
- Packet headers contain source and destination IPs for routing decisions
- Address formats balance human readability with machine processing requirements
- Networks use address translation to connect private and public IP spaces
- Dynamic addressing allows efficient reuse of limited IPv4 address pools
The addressing system works seamlessly behind the scenes. When you learn what an IP address is, you recognise how this invisible infrastructure supports every online activity. From streaming services to cloud storage, IP addresses make digital communication possible by providing the addressing framework networks need to function reliably.
Different types and versions of IP addresses explained
The internet uses two primary IP versions with distinct characteristics. IPv4 and IPv6 differ in bit length, notation, and address pool size. IPv4 employs 32 bits formatted as dotted decimal notation, providing approximately 4.3 billion unique addresses. IPv6 uses 128 bits written in hexadecimal notation, offering roughly 340 undecillion addresses. This massive expansion solves the address exhaustion problem that plagued IPv4 as internet usage exploded globally.
IPv4 addresses look like 203.0.113.45, using four octets of decimal numbers from 0 to 255. IPv6 addresses appear as 2001:0db8:85a3:0000:0000:8a2e:0370:7334, using eight groups of four hexadecimal digits. The notation differences reflect the underlying bit structures, with IPv6's longer format accommodating exponentially more devices. Many networks now run both versions simultaneously during the transition period.
| Feature | IPv4 | IPv6 |
|---|---|---|
| Address length | 32 bits | 128 bits |
| Notation | Dotted decimal (192.0.2.1) | Hexadecimal (2001:db8::1) |
| Total addresses | ~4.3 billion | ~340 undecillion |
| Header complexity | Variable length | Fixed simplified header |
| Address exhaustion | Fully allocated | Abundant supply |
Beyond version differences, public and private IP addresses serve distinct purposes. Public IPs are globally unique and routable across the internet, assigned by ISPs to identify devices externally. Private IPs function only within local networks and cannot route publicly. Common private ranges include 192.168.0.0/16, 172.16.0.0/12, and 10.0.0.0/8 for IPv4. These reserved blocks allow organisations to create internal networks without consuming public address space.
Network Address Translation bridges private and public spaces. Your router uses NAT to translate multiple private IPs to a single public IP, allowing dozens of devices to share one internet connection. This technique extended IPv4's lifespan by reducing public address demand, though it introduces complexity for certain applications requiring direct connectivity.

The static versus dynamic distinction affects how addresses are assigned and managed. Static IPs remain permanently assigned to specific devices, providing consistent addressing for servers, network equipment, and services requiring reliable identification. Dynamic IPs are temporarily assigned via DHCP and can change when devices reconnect or leases expire. Most residential connections use dynamic IPs to optimise address pool utilisation.
Pro Tip: Check whether you have a static or dynamic IP by noting your public IP address, restarting your router, and checking again. If it changed, you have dynamic addressing.
Understanding these distinctions helps when troubleshooting connectivity issues or configuring network services. Key differences include:
- IPv4 exhaustion drives IPv6 adoption despite transition challenges
- Private addressing enables local networks without consuming public space
- Static IPs suit servers whilst dynamic IPs optimise residential connections
- NAT allows address sharing but complicates peer connectivity
- Dual stack networks run both IPv4 and IPv6 simultaneously
The comparison between IPv4 and IPv6 reveals why migration remains essential despite technical hurdles. IPv6's simplified header structure improves routing efficiency whilst its vast address space eliminates scarcity concerns. However, backwards compatibility requirements mean IPv4 will persist for years as organisations gradually transition infrastructure. Understanding both versions prepares you for the hybrid networking environment dominating current internet architecture.
The role of IP addresses in cybersecurity and online privacy
Your IP address reveals more than you might expect. IP addresses disclose approximate location, ISP, organisation, and sometimes specific network details that enable tracking and profiling. Websites, advertisers, and potential attackers use this information to build profiles, target content, or launch attacks. Geolocation databases map IPs to cities and regions with surprising accuracy, exposing your general whereabouts whenever you browse.
The privacy risks extend beyond simple location disclosure. Persistent tracking across websites becomes possible when your IP remains constant, allowing third parties to correlate browsing activity and build detailed behavioural profiles. Deanonymization attacks combine IP data with other information sources to identify individuals behind supposedly anonymous activities. Law enforcement and intelligence agencies routinely use IP addresses to trace online actions back to physical locations and specific internet accounts.
Carrier Grade NAT introduces unique privacy challenges. CGNAT shares one public IP amongst many users causing collateral damage in blocking. When one user engages in malicious activity, security systems may block the shared IP, affecting hundreds of innocent users simultaneously. This shared addressing model complicates accountability whilst creating false positives in security systems that assume one IP equals one user.
IP truncation attempts to preserve privacy by removing the final octets before storage or analysis. However, anonymization through truncation fails because remaining bits still provide sufficient information for identification, especially when combined with timestamps and other metadata. A truncated IP like 203.0.113.x still reveals ISP, general location, and enough data for correlation attacks.
Consider these cybersecurity implications:
- Geolocation enables targeted attacks based on regional vulnerabilities
- IP logging creates audit trails linking activities to specific connections
- Shared IPs in CGNAT environments complicate forensics and attribution
- Dynamic IP changes provide minimal privacy against sophisticated tracking
- VPNs and proxies mask real IPs but introduce trust dependencies
Pro Tip: Public Wi-Fi networks expose your IP to everyone on the same network, making it trivial for attackers to intercept traffic or launch man-in-the-middle attacks.
"In cybersecurity contexts, IP addresses serve as both identifiers and potential vulnerabilities. Whilst necessary for routing, they expose users to tracking, profiling, and targeted attacks that require active mitigation through privacy tools and secure networking practices."
The tension between functionality and privacy remains unresolved. Networks require IP addresses for routing, yet this necessity creates inherent privacy risks. Modern privacy tools like VPNs, Tor, and proxy services attempt to mask real IPs by routing traffic through intermediaries. These solutions introduce their own trust requirements, as VPN providers can theoretically log the same information they claim to protect.
Understanding IP privacy risks empowers informed decisions about online security. Recognising what your IP reveals helps you assess threats and choose appropriate protective measures. Whether you're a casual user concerned about tracking or a security professional defending networks, IP address privacy considerations shape how you approach online activities and implement safeguards.
How IP address allocation and transfers impact internet infrastructure
The IPv4 address pool reached exhaustion years ago, fundamentally changing how organisations acquire addresses. Regional Internet Registries no longer have IPv4 blocks to distribute freely, forcing organisations to purchase addresses through transfer markets or accelerate IPv6 deployment. This scarcity created a secondary market where IPv4 addresses trade at $50 to $65 per address, with 8,062 transfers totalling 81.93 million addresses in 2025 alone.
IPv6 allocation follows different principles designed to prevent exhaustion. IPv6 allocations start at /32 for Local Internet Registries, using HD-Ratio metrics (0.94) for efficiency. This generous allocation strategy ensures organisations receive sufficient address space for growth without artificial scarcity. The /32 prefix provides 4.3 billion /64 subnets, enough for most organisations' foreseeable needs. This abundance contrasts sharply with IPv4's constrained environment.
The transfer market statistics reveal infrastructure pressures. Empirical data shows IPv4 allocated pool reached approximately 3.685 billion addresses in 2023, with the available pool contracting as demand persists. IPv6 assignment durations trend longer as organisations commit to the newer protocol, whilst IPv4 transfers remain active despite high prices. This dual reality reflects the internet's transitional state between protocols.
| Metric | IPv4 | IPv6 |
|---|---|---|
| Total allocated addresses | ~3.685 billion | Effectively unlimited |
| New allocations | Via transfers only | Direct from RIRs |
| Typical allocation size | /24 (256 addresses) | /32 (4.3B subnets) |
| Market price per address | $50-$65 | No market (free from RIRs) |
| 2025 transfer volume | 81.93M addresses | Not applicable |
These infrastructure realities affect organisations differently based on size and needs. Startups launching new services face high IPv4 acquisition costs, incentivising IPv6-only or IPv6-primary architectures. Established enterprises maintain legacy IPv4 infrastructure whilst gradually adding IPv6 support. Cloud providers operate dual-stack environments, offering both protocols to accommodate diverse customer requirements.
The allocation efficiency metrics matter for long-term planning. HD-Ratio calculations ensure IPv6 space gets utilised effectively without the wasteful allocation patterns that contributed to IPv4 exhaustion. By requiring organisations to demonstrate utilisation before receiving additional space, registries prevent hoarding whilst ensuring legitimate growth needs are met. This balanced approach learned from IPv4's mistakes.
IT professionals must navigate this complex landscape when planning network infrastructure. IPv6 adoption benefits include abundant addressing, simplified configuration through autoconfiguration, and future-proofing against IPv4 scarcity. However, transition costs, training requirements, and compatibility concerns slow adoption rates despite clear long-term advantages.
The transfer market's existence highlights both IPv4's value and its limitations. Organisations pay premium prices for a finite resource whilst a superior alternative remains underutilised. This economic inefficiency will eventually resolve as IPv6 deployment reaches critical mass, but the transition timeline remains uncertain. Current projections suggest dual-stack operations will persist throughout the decade as legacy systems gradually retire.
Understanding allocation dynamics helps organisations make informed infrastructure decisions. Whether acquiring IPv4 addresses through transfers, planning IPv6 deployment, or operating dual-stack networks, recognising the supply constraints and allocation policies shaping address availability proves essential for effective network planning and budget forecasting.
Explore IP lookup tools to enhance your understanding
Now that you understand how IP addresses function, their types, security implications, and infrastructure challenges, practical tools can help you apply this knowledge. Discovering your current IP address and associated details provides immediate insights into your online presence and potential privacy exposure.
Our IP address lookup tool reveals your public IP, ISP, location data, and network details in seconds. Understanding what information your IP broadcasts helps you make informed privacy decisions. The IP to location finder shows precisely what geographic data websites and services can determine from your connection.
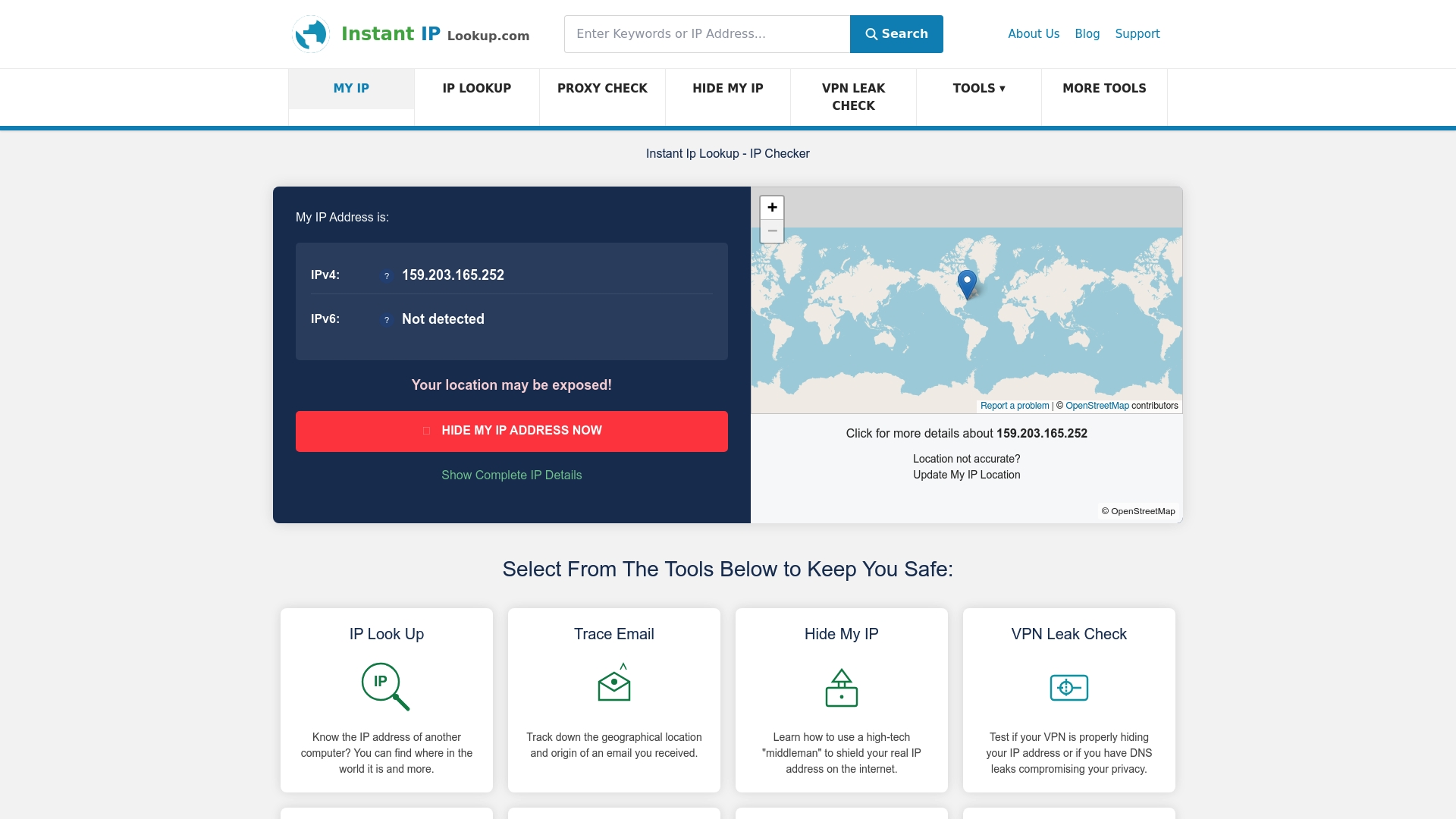
If you use VPN services for privacy protection, our VPN leak check verifies whether your real IP remains hidden or accidentally leaks through DNS, WebRTC, or other channels. These practical tools transform theoretical knowledge into actionable security insights, helping you verify your privacy measures work as intended and understand your digital footprint.
What is an IP address?
What exactly is an IP address?
An IP address is a unique numerical identifier assigned to devices on networks using Internet Protocol. It serves two purposes: identifying the device and providing its network location for routing data packets. Think of it as a postal address that allows information to find its destination across the internet.
How can I find my IP address?
You can discover your public IP address by visiting any IP lookup service in your web browser. For your local private IP, check your device's network settings under Wi-Fi or Ethernet connection details. Most operating systems display this information in network configuration menus.
What is the difference between IPv4 and IPv6?
IPv4 uses 32-bit addresses providing about 4.3 billion unique combinations, written as four decimal numbers like 192.0.2.1. IPv6 uses 128-bit addresses offering 340 undecillion combinations, written in hexadecimal like 2001:db8::1. IPv6 was created to solve IPv4 address exhaustion.
Can someone track me using my IP address?
Yes, your IP address reveals your approximate geographic location, ISP, and organisation. Websites use this for tracking, targeted advertising, and content personalisation. Whilst it doesn't provide your exact street address, it enables profiling and can be combined with other data for identification.
Why do I need to hide my IP address?
Hiding your IP address protects privacy by preventing websites from tracking your location and browsing patterns. It helps bypass geographic content restrictions, avoid targeted attacks based on your location, and maintain anonymity online. VPNs and proxy services mask your real IP by routing traffic through intermediary servers.
What happens when IPv4 addresses run out?
IPv4 addresses have already been exhausted at the registry level. Organisations now acquire them through transfer markets at premium prices or deploy IPv6, which offers virtually unlimited addresses. Most networks operate dual-stack systems supporting both protocols during the transition period.
